|
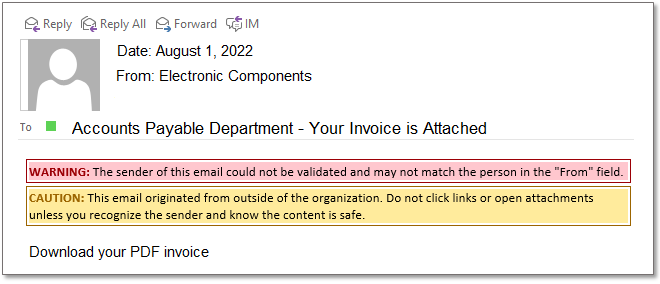
We've all seen the red highlighted message at the top of an email, "CAUTION! IF THIS EMAIL ORIGINATED OUTSIDE OF THE ORGANIZATION DO NOT CLICK ON ANY LINKS". Does your Accounts Payable Process rely on suppliers emailing invoices to your business and your AP Staff then open each email one-by-one, download a PDF or file to their computer and then print each invoice to paper. "EMAIL IS THE NUMBER ONE METHOD USED BY HACKERS TO EXPLOIT AN ORGANIZATIONS INFRASTRUCTURE, GAIN ACCESS AND STEAL INFORMATION" An AP Automation platform like, "Vision360 Enterprise", eliminates the need for AP Staff to open emails, download PDF files and print invoices. This dramatically reduces the risk of fraudulent emails exposing an organization to potential hacking or phishing schemes. In addition, this is an incredible time saver by reducing the amount of time and energy it takes an AP Department to open and print emails. An AP Automation platform like "Vision360 Enterprise" will apply a series of business rules and validations against the incoming invoices to further ensure that they are being submitted from "legitimate vendors". By having centralized processing coupled with consistent internal controls that are applied systematically and not relying on human intervention the risk of potential fraud is greatly reduced. What are computer hackers? Computer hackers are people who break into internet-connected devices such as computers, tablets and smartphones, usually with the intent to steal, change or delete information. Just as other thieves have malicious intent, hackers usually find their way into devices for negative purposes. (However, one exception is so-called white hat hackers, whom companies hire to break into their devices to find security flaws that need to be fixed.) Hackers may want to steal, alter or delete information in your devices, and they often do so by installing malware (software used for malicious purposes) you might not even know is there. These thieves might get access to your most precious data before you’re aware of a break-in. Types of hacking: Ransomware is on the rise! Here are some of the reasons computer hackers break into devices:
Accounts Payable Automation systems can modernize your invoice processing by reducing risk, providing cost control and increasing efficiencies. Please consider registering for one or our informational webinars or contact us directly for more information.
0 Comments
You advertise for an open AP Specialist position. The ad reads something like this: Description Our team is seeking an Accounts Payable (AP) Specialist who will be responsible for processing (i.e., coding and entering) and paying vendor invoices and employee expenses in a timely manner. Essential Functions
You seek a candidate with relevant job experience, skilled in accounting practices, they will be involved in the cash flow for your business, the need to make quick business decisions that effect your supply chain and vendor relationships. However, with all this in mind, they will spend between 40 - 60 percent (or more) of their day manual keying invoices into the financial system for payment processing. Seems like all this experience could be used to better serve the business and their interest in a career in accounting. You went through the process of advertising (costs money), interviewing candidates (costs time & money), hiring and training the new hire (costs time and money) and in the end they spend more time keying invoices than any other function. Does manual invoice keying make the best use of your AP Staff's time?
|
AuthorVision360 Enterprise Accounts Payable Automation Solution by BlueCreek Software reduces time wasted chasing down paper invoices by automating invoice approvals, eliminating manual data entry, eliminating paper invoices and reducing processing costs. Categories
All
Archives
September 2023
|

 RSS Feed
RSS Feed